General information
Versions Affected:
WILY_INTRO_ENTERPRISE 9.7
WILY_INTRO_ENTERPRISE 10.1
WILY_INTRO_ENTERPRISE 10.5
WILY_INTRO_ENTERPRISE 10.7
Vendor URL: https://sap.com
Bug: Hard-coded Credentials
Reported: October 21, 2021
Date of Public Advisory: October 28, 2021
Reference: SAP Security Note 2971638
Author: Arpine Maghakyan (RedRays)
Description
ADVISORY INFORMATION
Title: Patch bypass for [CVE-2020-6369] Hard-coded Credentials in CA Introscope Enterprise Manager
Advisory: [RedRays-21-011]
Risk: Medium
Date published: 22.08.2022
VULNERABILITY INFORMATION
Remotely Exploitable: Yes
Locally Exploitable: No
CVSS Information
CVSS v3 Base Score: 7.5 / 10 (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N)
VULNERABILITY DESCRIPTION
CA Introscope Enterprise Manager’s releases 10.7.0.306 or lower, allow unauthenticated attackers to bypass the authentication if the administrator has not changed the default passwords for Admin and Guest. This may impact the confidentiality of the service.
TECHNICAL DESCRIPTION
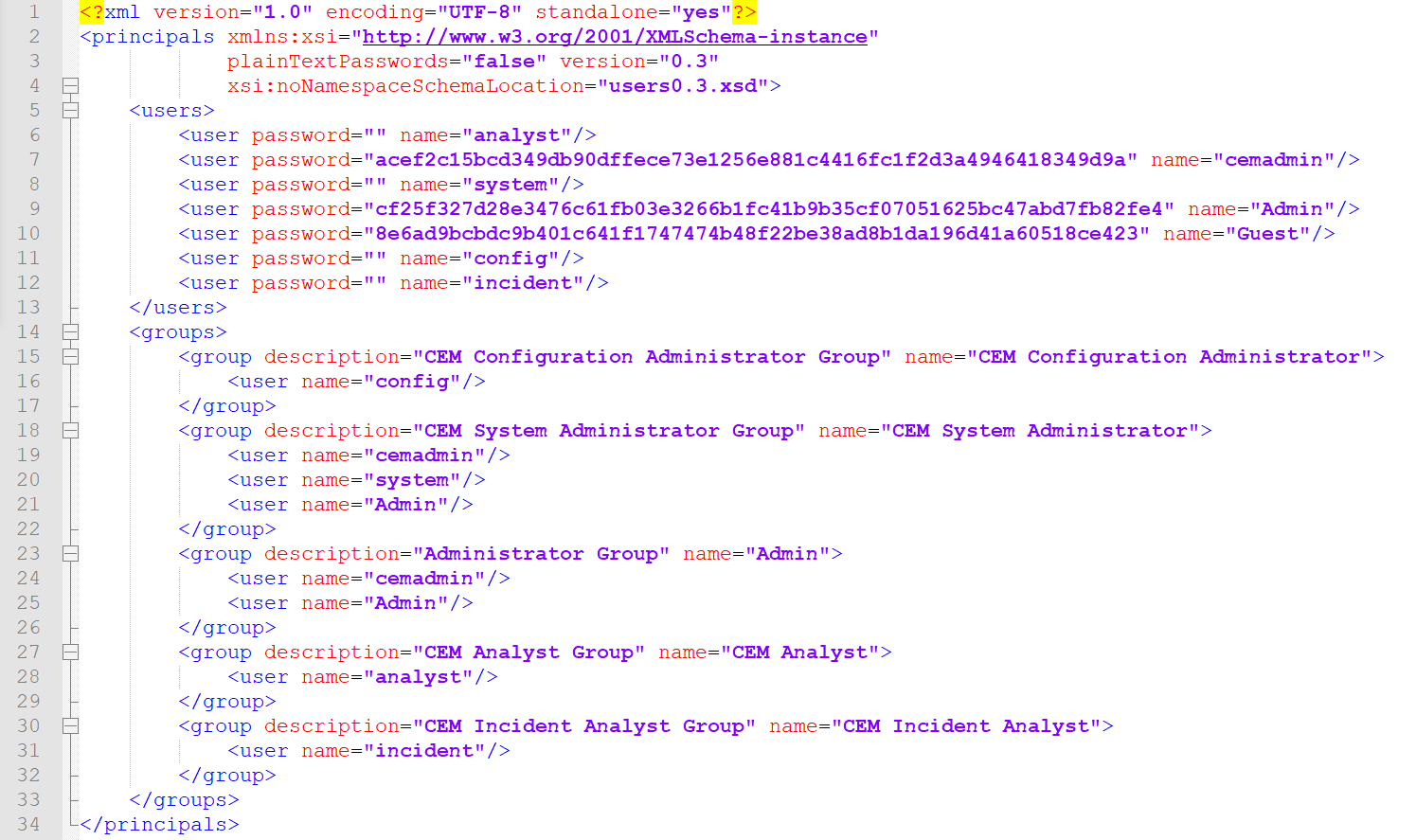
The CA Introscope Enterprise Manager has the following configuration file with hardcoded usernames and hashed passwords.
In 2020, SAP Fixed hard-coded Credentials in CA Introscope Enterprise Manager, fixed passwords for Guest and Admin users, and forgot to remove the hardcoded passwords for cemadmin users.
We analyzed the hash and found the right password for the hash for the cemadmin user.
Cemadmin:acef2c15bcd349db90dffece73e1256e881c4416fc1f2d3a4946418349d9a:quality
Admin:cf25f327d28e3476c61fb03e3266b1fc41b9b35cf07051625bc47abd7fb82fe4:Admin89
Guest:8e6ad9bcbdc9b401c641f1747474b48f22be38ad8b1da196d41a60518ce423:guest12
sapsupport:f18335c36cccfb60f640db4a56c18634949882d2ce8de468fe2c1d0806b778c:(String)null
ABOUT RedRays
The main goal of RedRays is to narrow the security gap in both the technical and business realms. The company offers solutions to examine and protect SAP, Oracle, and Microsoft ERP systems against cyberattacks and internal fraud.
Typically, our customers are big organizations and managed service providers whose needs include the active monitoring and management of security across extensive SAP environments worldwide.
ABOUT RedRays R&D
The company’s competence is founded on RedRays’ research section, which specializes in vulnerability research and analysis of essential corporate applications. It has received several accolades from major software companies, including SAP, Oracle, Microsoft Dynamics, and IBM.
Experts from RedRays have been asked to lecture, present, and train at major international security conferences on all continents.
Address: Casablanca, Morocco
Phone: (+32)489-16-78-85
Twitter:@redraysio