We pointed our ABAP Code Scanner at a handful of production SAP systems over the past month. 30+ real vulnerabilities came out. Not theoretical stuff from a checklist - actual SQL injections, hardcoded credentials, and missing authority checks sitting in custom ABAP code that had been running in production for years.
None of these were caught by manual code review. None were flagged by transport checks. They were just there, waiting.
What the scanner checks for
164 rules, built from real findings on real SAP systems. Not generic patterns copied from OWASP - these are ABAP-specific checks that know about AUTHORITY-CHECK, OPEN DATASET, EXEC SQL, RFC destinations, BSP controllers, Web Dynpro, CDS views, and all the other places where SAP developers make security mistakes. Here are the main categories.
SQL Injection & Code Injection (ABP-001 to ABP-025)
Dynamic SELECT with string concatenation in WHERE clause, native SQL via EXEC SQL with user input, ADBC (CL_SQL_STATEMENT) with dynamic queries, AMDP SQLScript injection, GENERATE SUBROUTINE POOL from user data, INSERT REPORT with dynamic content. Also catches dynamic CALL METHOD, CALL FUNCTION, PERFORM, CREATE OBJECT, and SUBMIT where the target name comes from user input. 25 checks covering every way you can inject code or SQL in ABAP.
OS Command & File System (ABP-026 to ABP-041)
CALL 'SYSTEM' with user-controlled commands, SXPG_COMMAND_EXECUTE without input validation, pipe injection via OPEN DATASET ... FILTER. For file operations: OPEN DATASET, READ DATASET, DELETE DATASET with paths from user input, missing ../ checks, ZIP extraction without path validation. Also catches client-side attacks through CL_GUI_FRONTEND_SERVICES and SAP Shortcut (.sap file) injection.
RFC & Network (ABP-042 to ABP-056)
Dynamic RFC destinations from user input, missing whitelist for RFC targets, trusted relationship abuse, DESTINATION 'NONE' for authorization bypass, RFC callbacks without source validation. HTTP checks: user-controlled URLs in CL_HTTP_CLIENT, missing host whitelists, LDAP injection, HTTP instead of HTTPS, disabled SSL certificate validation. Catches SSRF patterns specific to SAP.
Web Layer - BSP, Web Dynpro, ICF (ABP-057 to ABP-075)
BSP output without HTML escaping, BSP controllers and actions without authorization, Web Dynpro FormattedTextView with unescaped content, WD supply functions and action handlers missing auth checks, ICF handler responses without escaping, CSRF in HTTP handlers, JWT weaknesses, CRLF header injection, email content injection. 19 checks covering the SAP web stack.
Missing Authorization (ABP-076 to ABP-096)
Missing AUTHORITY-CHECK before CALL TRANSACTION, SUBMIT, RFC calls, file operations (S_DATASET), repository access (S_DEVELOP). Missing auth in RFC-enabled function modules, BAPIs, Web Dynpro components, BSP controllers, ICF handlers, OData DPC extensions. Also: ignored SY-SUBRC after authority check, missing ACTVT field, dummy values in auth checks, VALUE '*' wildcards, dynamic auth object names, CDS views without access control.
Backdoors & Logic Bombs (ABP-097 to ABP-108)
Hardcoded username checks (IF SY-UNAME = 'ADMIN'), system ID checks (SY-SYSID), client-specific bypasses (SY-MANDT), date/time-triggered code, hidden parameters, authorization bypass for specific users. Also catches obfuscation via macros and suppression of security audit findings with pseudo-comments. These are the checks that find intentional backdoors planted by developers or consultants.
Data Integrity & Cross-Client (ABP-112 to ABP-125)
DROP TABLE/TRUNCATE via native SQL, direct modification of standard tables (MARA, VBAK, EKKO), DELETE FROM and UPDATE without WHERE clause, mass deletion without confirmation. Cross-client attacks: SELECT CLIENT SPECIFIED with user input, cross-client INSERT/UPDATE/DELETE. Transaction integrity: COMMIT WORK in RFC modules, missing ENQUEUE lock checks.
Secrets, Logging & Crypto (ABP-126 to ABP-164)
Hardcoded passwords, API keys, and encryption keys in source code. Sensitive data in log output (MESSAGE, WRITE, BAL application log). Missing security audit log for sensitive operations. Weak crypto (MD5/SHA1 for passwords, insecure random via CL_ABAP_RANDOM). Unsafe deserialization (IMPORT FROM DATA BUFFER with external data). XML External Entity (XXE) via CALL TRANSFORMATION without DTD disabled. Debug statements (BREAK-POINT) left in production code.
Why this keeps happening
SAP security teams focus on patching, configuration, and user authorization. That's the right priority. But custom ABAP code is a blind spot. Most organizations have no process for reviewing it - not during development, not during transport, and definitely not after it's been running in production for years.
Manual code review doesn't scale. A typical SAP system has 500K+ lines of custom ABAP. Nobody is going to read all of that. Static analysis tools exist for Java and C, but ABAP has been ignored by the mainstream AppSec world because it's a niche language running inside a niche platform.
That's the gap we built the scanner for.
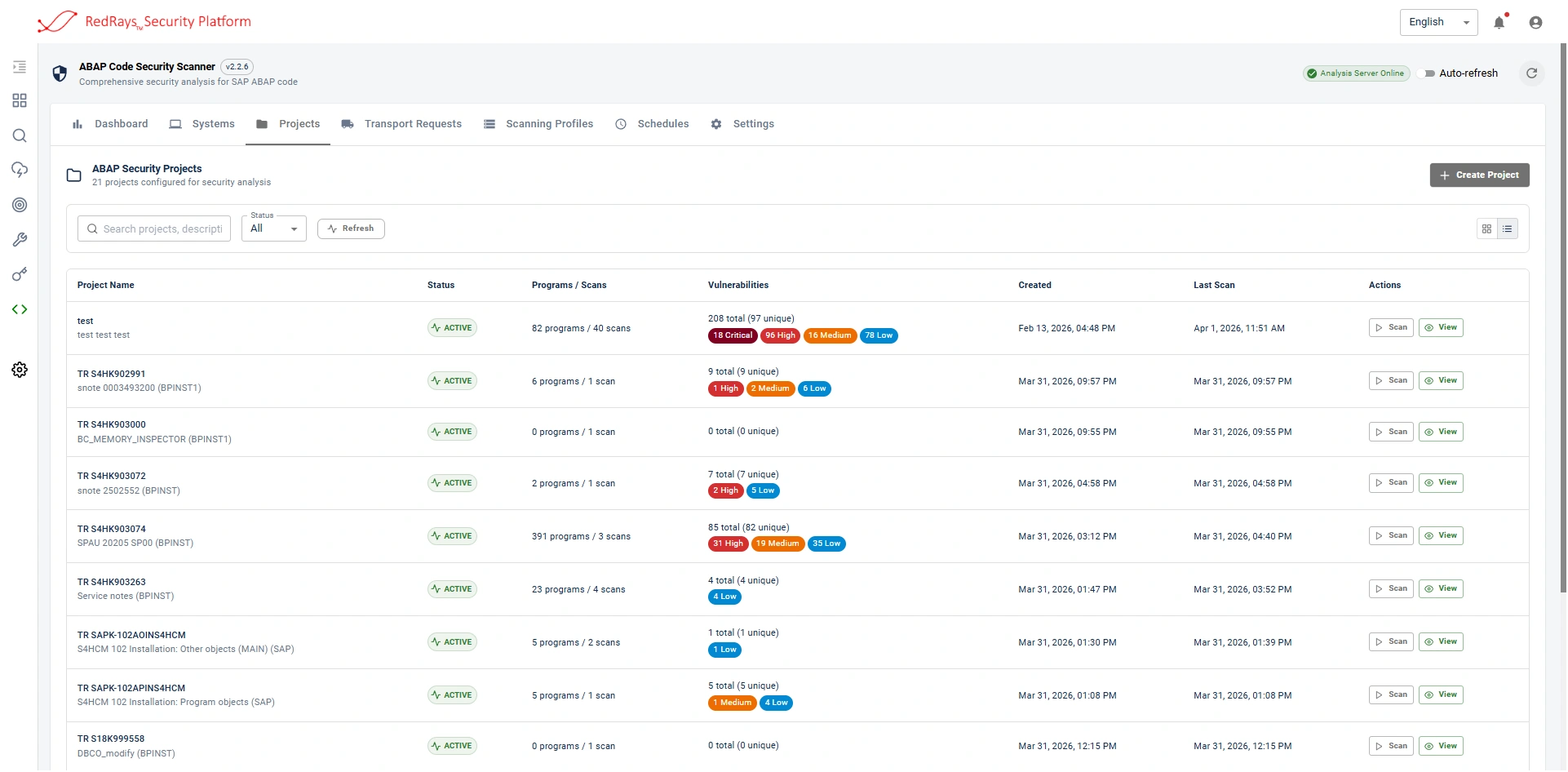
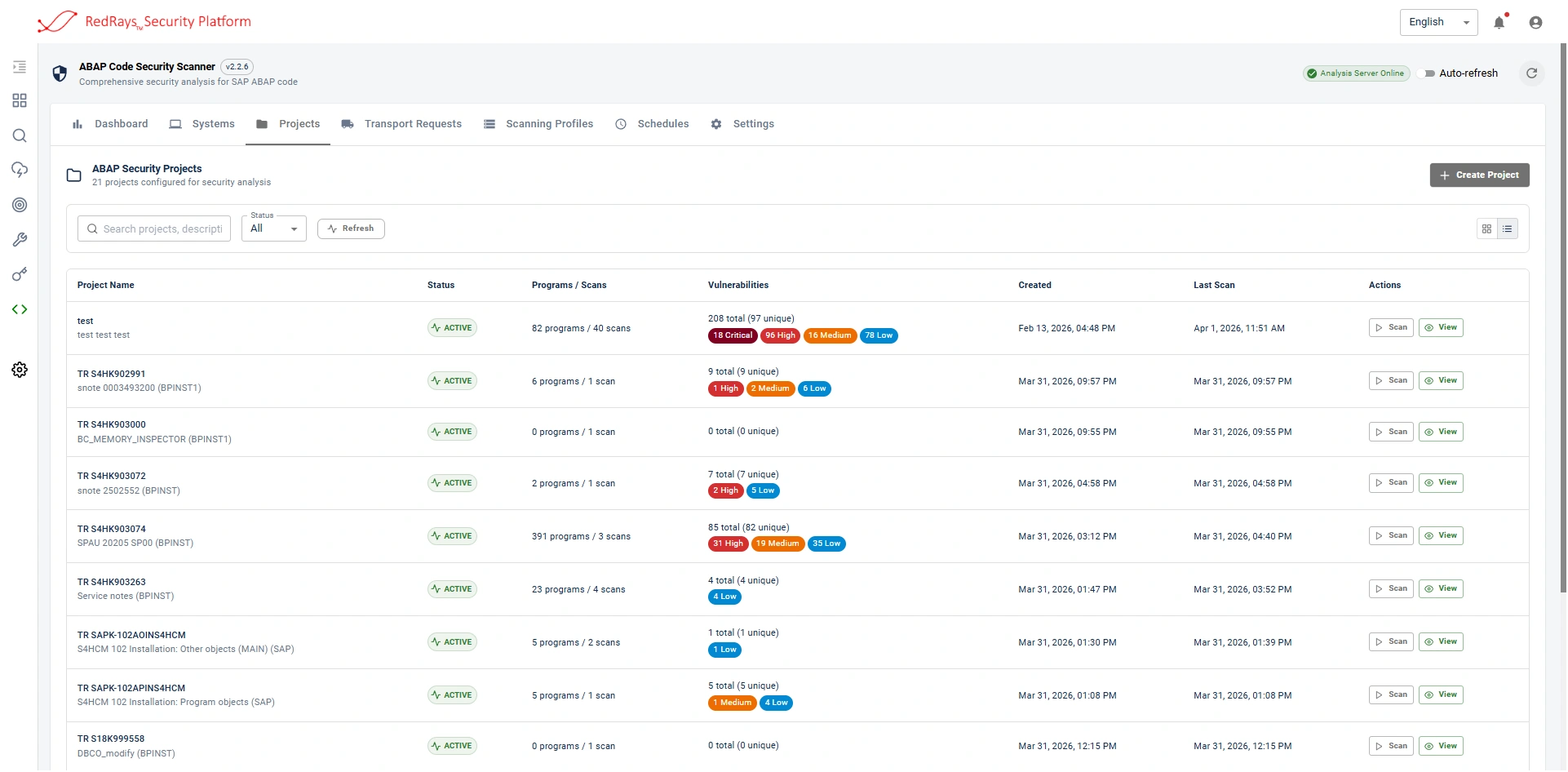
How the scanner works
1. Connects to your SAP system via RFC (read-only access to source code)
2. Pulls all custom ABAP programs, includes, function modules, classes
3. Runs static analysis: taint tracking, pattern matching, data flow analysis
4. Reports findings with exact line numbers, risk rating, and fix guidance
5. Takes about 15 minutes for a typical system with 100K lines of custom code
164 checks across 10 categories: injection (SQL, code, OS command), file system attacks, RFC/network security, web layer (BSP, Web Dynpro, ICF), missing authorization, backdoors, data integrity, cross-client access, secrets management, and crypto weaknesses. Every rule is specific to ABAP and SAP.
The offer
2 weeks of full access. Free.
We also provide a demo SAP system if you want to try the scanner without connecting your own. No setup needed on your side - we give you the credentials, you log in and scan.
No credit card. No auto-renewal. No sales calls unless you ask for them.
If you're an SAP Basis admin, security consultant, auditor, or developer working with ABAP code, this is a good way to see what's hiding in your custom programs.
Try the scanner on your ABAP code
Free 2-week trial. Demo SAP system included. Set up within 24 hours.
[email protected]





